As noted in our blog post in February, we wished to provide an update on the email authentication changes brought in by Google and Yahoo. Over the past few months, we have worked with many clients to ensure to the delivery of the email to reduce the likelihood and impact of the cause of this. […]
Category Archives: Support
You might have seen recent announcements about crucial enhancements and requirements aimed at bolstering email security and ensuring successful delivery to Google and Yahoo email addresses. These changes are designed to refine the email authentication process, safeguard against spam, and verify the authenticity of senders. The key components of these changes involve the implementation of […]
A new vulnerability in the Microsoft Support Diagnostic Tool in Windows has been identified. Known as CVE-2022-30190 or the Follina bug, allows hackers to bypass security measures in place to protect users from phishing emails. Phishing emails are designed to trick the user into clicking on a malicious link. When Microsoft suspects a phishing email […]
Just when you thought 2021 was done throwing curveballs at us, along comes one of the biggest cybersecurity vulnerabilities in recent memory. Log4j is a piece of open-source software, which has been incorporated into many software apps. Recently it was discovered that Log4j could be exploited to bypass the usual authentication processes and give cyber […]
Google Chrome has been in the news over the past few weeks, and not all the reporting has been entirely accurate. So, what’s fact and what’s fiction? Here we answer a few common questions that have come up as a result of various media reports and social media commentary. Did Google really advise users […]
Did you know that Queensland accounted for 30% of all cyber crimes reported in the last financial year, the most of any state or territory in Australia? Cyber crime also increased, with report made every eight minutes in Australia, compared to one every 10 minutes previous financial year. Self-reported losses totalled more than $33 billion. […]
Google has released critical security updates for all Google Chrome users on Windows, Mac and Linux desktops and laptops. These security updates to address two security vulnerabilities on 17 June 2021. If these updates are not applied then hackers could exploit the vulnerabilities to gain access to your device. CyberGuru’s managed services clients will receive […]
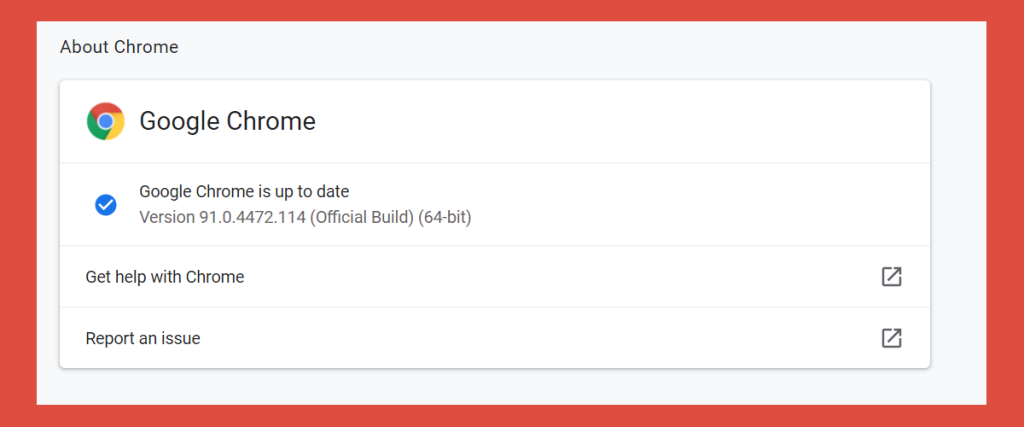
It has been over five years since Microsoft launched the original release of Windows 10 and there have been many improvements over this time. Announced that it would be the “last ever version of Windows”, Microsoft have provided regular Feature Updates, generally a few times a year, bringing new features and enhancements, as well as […]
We have received advice released from auDA, the .au domain administrator, of a phishing scam targeting .au domain name registrants via email. The emails are of someone posing as an auDA employee and requesting copies of personal documents, including photo identification and a Medicare Card to a nominated email address. If you receive an email […]
In the past few weeks, you may have read news of Microsoft Exchange servers being hacked by state-sponsored actors. It has come to light that four previously unidentified vulnerabilities had been identified and were being exploited by hackers in widespread attacks. What does this mean for businesses and personal users? To understand the impact, we […]